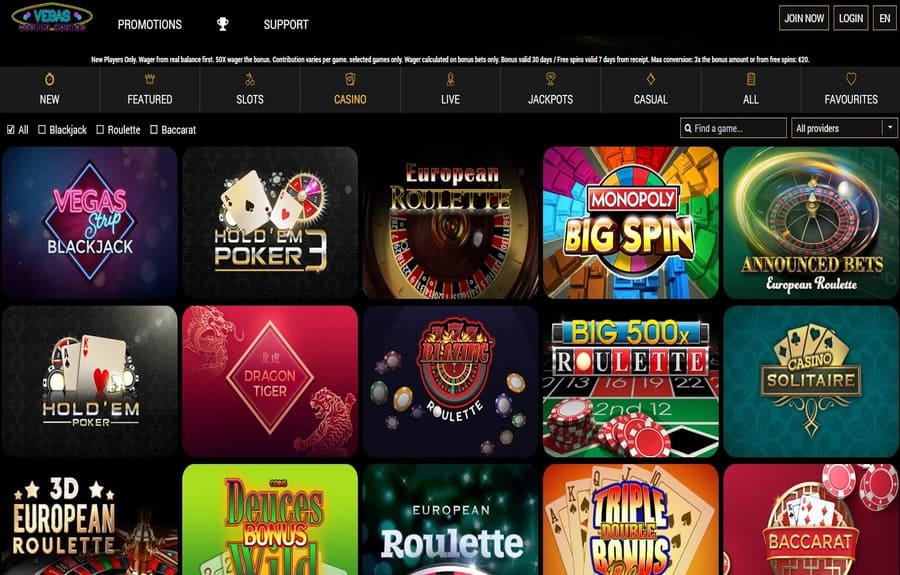
행운을 시험해보세요! 카지노사이트로 즐기는 다채로운 이벤트
카지노사이트에서 즐길 수 있는 무한한 즐거움! 쿠폰, 이벤트, 프로모션, 보증까지 모두 한 자리에서 만나보세요. 어디에서도느낄 수 없는 특별한 혜택들이 여러분을 기다리고 있습니다. 이제 당신의 운을 시험해보는 좋은 기회가 찾아왔습니다. 쿠폰을 활용하여 더 많은 혜택을 누려보세요. 특별한 할인 혜택부터 무료 게임까지, 다양한 쿠폰을 만나보실 수 있습니다. 더 이상 지출에 걱정할 필요가...